Comments
In the same slideshow, CMG counted Facebook, Google, and Amazon as clients of its “Active Listening” service. After 404 reached out to Google about its partnership, the tech giant removed the media group from the site for its “Partners Program,” which prompted Meta, the owner of Facebook, to admit that it is reviewing CMG to see if it violates any of its terms of service.
So not just Facebook.
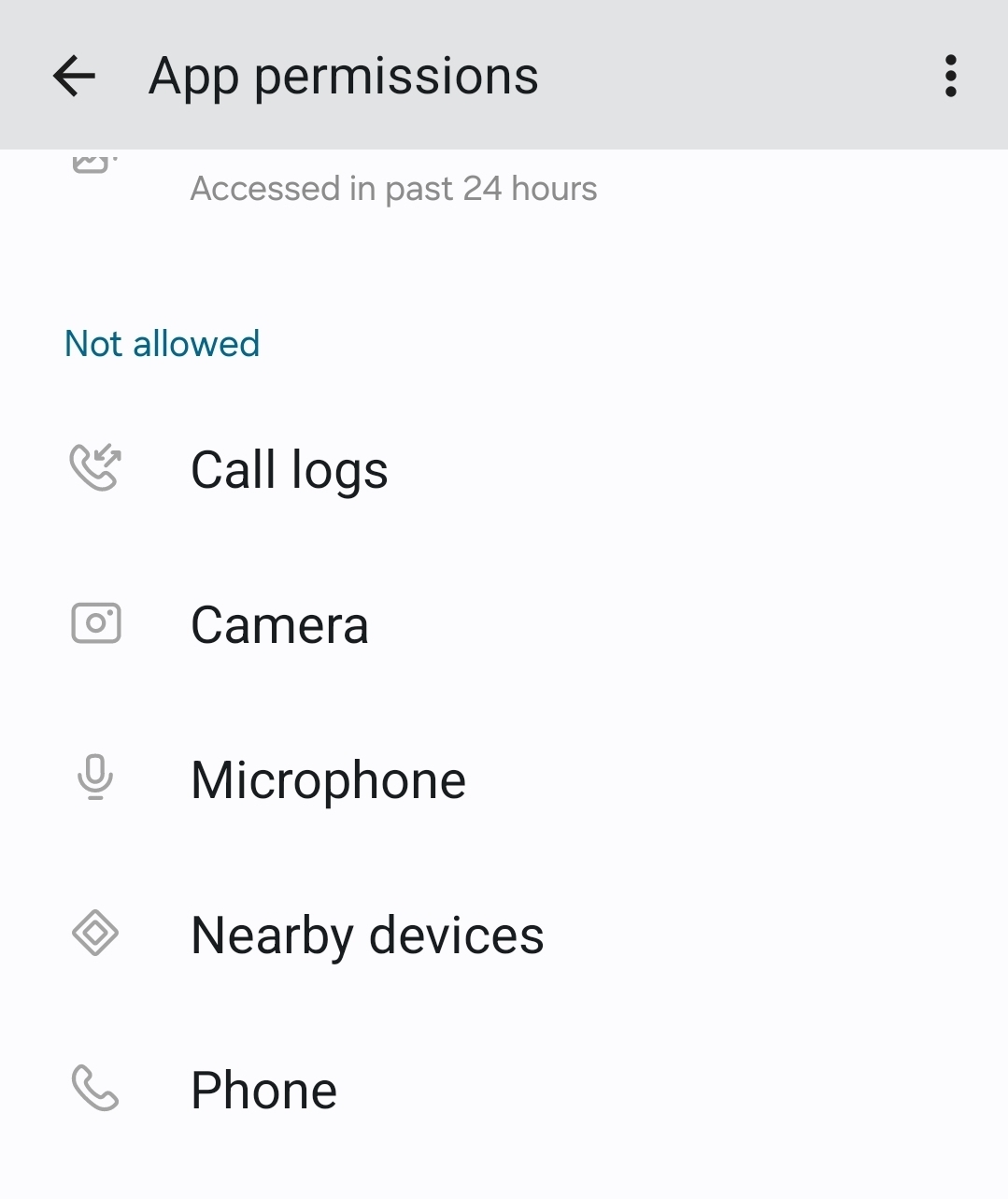
This is why app permissions are a thing.
Would this trigger the ‘mic in use’ indicator on Android and iPhone platforms?
If it existed, yes. They probably didn’t realize before making this failed “pitch”, which is why they never developed this.
It has to. The only way that it wouldn’t trip the indicator is if it was built into the operating system itself or somehow had an exploit to get around OS security protections.
The information is fascinating but by and large should no longer be applicable because the OS has been designed to prevent using the microphone without the users knowledge. An app doesn’t have access to the microphone hardware without going through the OS first. Google could modify the OS to do such a thing, but of course, they have to hide this in the proprietary parts of Android, and the generally open nature of the platform give security researchers quite good access to observe such activity. I’d be surprised such activity would go unnoticed. It seems unlikely.
I think this type of approach might have worked on older OS versions but I don’t see how it could work today in general.
Starting with version 12, the Android operating system introduced a limit of 200Hz to help mitigate such attacks, but as you indicate research shows that some reconstruction may be possible in some scenarios. This is an ongoing area and future mitigations continue to be considered.
From Kaspersky:
In 92% of cases, the accelerometer data made it possible to distinguish one voice from another. In 99% of cases, it was possible to correctly determine gender. Actual speech was recognized with an accuracy of 56% — half of the words could not be reconstructed.
The monitoring application would also need to run in the foreground to access the data on a continuous basis.
Overall it does look like an interesting theoretical concern.
Here’s an exotic conspiracy theory: advertisers are performing sensor fusion / superresolution on many colocated gyrophones to exceed the per-device 200Hz cap. Phone clocks are certainly not aligned to the millisecond, so this would enable them to get a higher time resolution.
Don’t think so. Wait until you find out what your smart TV is doing.
Nah it got banned from the network when it started inserting ads into my YouTube feed that I already pay for.
Heh. My TV has never been online, not even once. I’d rather suffer the occasional firmware bug than have it act as a sensor.
a lot of people called me crazy for saying that.
google does it too.
apple definitely does it too.
I’m not crazy about ads, it can be nice when they’re effective for the right reasons. That said, a break in happened at my estate once and the only evidence I needed or could secure was because I left my phone at home that day
Someone that still uses Facebook should post this there
It’ll probably get removed due to misinformation
Still worth it
Do we have any info about this being used by any app, or any details about the tech at all? We have an archived version of a deleted ad from a suspicious company. Do we know it even exists and wasn’t a prospective ad to judge interest that went nowhere?
Yeah, that’s how you creep me the fuck out and I don’t buy your shit.
Good luck.
Can someone develop a tool that automatically screens TOS and small print for apps and warns you of agreeing to shit like this?
Can’t wait for all the seven day old accounts to pop up and explain how this is actually just the magic algorithm and confirmation bias at work.
Wasn’t this a thing like 1-2 years ago, that was completely unverified, from a different Facebook advertiser?




