Southwest Airlines, the fourth largest airline in the US, is seemingly unaffected by the problematic CrowdStrike update that caused millions of computers to BSoD (Blue Screen of Death) because it used Windows 3.1. The CrowdStrike issue disrupted operations globally after a faulty update caused newer computers to freeze and stop working, with many prominent institutions, including airports and almost all US airlines, including United, Delta, and American Airlines, needing to stop flights.
Windows 3.1, launched in 1992, is likely not getting any updates. So, when CrowdStrike pushed the faulty update to all its customers, Southwest wasn’t affected (because it didn’t receive an update to begin with).
The airlines affected by the CrowdStrike update had to ground their fleets because many of their background systems refused to operate. These systems could include pilot and fleet scheduling, maintenance records, ticketing, etc. Thankfully, the lousy update did not affect aircraft systems, ensuring that everything airborne remained safe and were always in control of their pilots.
That makes fuckall sense.
Windows 3.1 not being updated by Microsoft has nothing to do with Crowdstrike rolling out an update to their Falcon Sensor software including a file with 42kB of zeroes.
On Windows 3.1 you probably can’t run Falcon Sensor, so in that way it could be related. But it seems way more likely that Southwest Airlines simply didn’t use Falcon Sensor on their normal Windows 10 or whatever clients.
There are probably competitors to Crowdstrike, at least some companies would be customers to one of them.
Or, for your consideration, could it perhaps be because they don’t use crowdstrike?
Yeah, what? 3.1 not getting updates has nothing to do with this. Software developed for 3.1 can still be updated. This article is just silly.
deleted by creator
If they still use Windows 3.1 and it works, then I do have to wonder about the rest of their security setup.
Windows 3.1 can’t use modern versions of tls which means it’s effectively impossible to network it securely.
You just know there’s an SMB share somewhere with no password, where files filled with unencrypted customer details get dumped for processing by an ancient AS400 server.
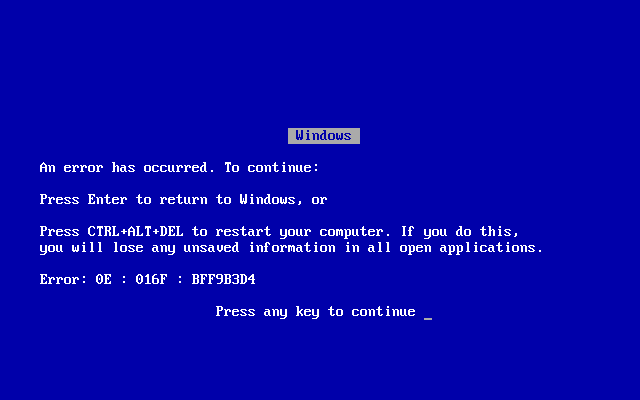
Windows 3.1 didn’t have the BSOD. It just froze. I remember with Windows NT 4, when we first got the BSOD, being so grateful that Microsoft decided to actually tell us that our computer wasn’t going to recover from the error. Otherwise, we’d just be sitting there, waiting, hoping it would unfreeze itself.
It never did
I think that NT 3.51 had a blue screen of death
Are you sure? I remember a long time ago being able to trigger a BSOD by opening Windows Calculator and dividing any number by 0. And I’m pretty sure that was 3.1 or 3.11.
In fact, I remember being able to change the color of the BSOD.
As another user mentioned, the BSOD first came in Windows NT 3.51.
But it definitely wasn’t in Windows 3.1 or Windows 3.11
The other user is wrong. I clearly remember the BSoD in Windows 3.1. You can find it easily with a simple web search. Here it is:
Hell, there were even memes of it:
Edit: I provided proof and was still downvoted lol. This place is quickly turning into reddit.
Windows 3.1 did have a BSOD. It wasn’t always fatal, you could try to hit enter to go back to Windows, but most of the time it wasn’t really recoverable, Windows often wouldn’t work right afterwards.
I ran into them all the time in 3.11 on our 486 which had some faulty RAM (the BSOD would even be scrambled). If we could get back to Windows after that, it’d just be in a zombie state where moving the mouse around would paint stuff over whatever was left on screen, and wouldn’t respond to clicks or keypresses.
Fun times.
IIRC Windows 95 did that as well
The fact that they’re running 3.1 is not something to be proud of. They’re probably extremely vulnerable to any other attack.
Quite the opposite.
Please explain. I’ll make 🍿
Microsoft’s Wolverine for the TCP stack was not available until Windows 3.11. An argument could be made that these systems are defacto air-gapped as they cannot communicate with modern networking.
Youre assuming the article is using “windows 3.1” to mean the exact version of the OS, instead of just the proper name of the OS overall. That probally unlikley.
Since lacking a network stack tends to limit usability, unless the systems are intentionally air gapped they likely are on windows 3.1.1 or later. Based on Southwest extensively documented and decades long IT neglect that landed its current COO in front of Congress for a previous days long outage, i doubt the systems are intentionally airgapped, as that implies a working and well funded IT department.
Just because it doesn’t have TCP/IP doesn’t mean there isn’t networking. Networks existed before the Internet and its Internet Protocol after all. It wouldn’t be so much air gapped as so archaic that only the most targeted attacks would work, and only if there is an infected PC acting as an intermediate between the Internet and ye olde network. Chances are it was never connected to the modern Internet as the technologies just aren’t compatible.
Old doesn’t mean secure. Those old systems have had decades since the last security patch. Even then computer security was barely a consideration for the developers.
I am not saying it is, normally old systems are the least secure. The bit you’re not getting is that this system is almost certainly air gapped, just not by choice. It can’t work with modern networks. It can’t work with modern viruses. Any exploit a modern hacker would think to use probably doesn’t exist yet. It’s a bit like trying to break someone’s car by putting sugar in the fuel, except they ride a horse. Do you get it yet?
Everything we know about this is that it was a disaster waiting to happen. Why the heck aren’t the airlines using Linux instead of Windows for critical stuff? How about something like…Chrome OS? Then you don’t need CrowdStrike because your OS is already secure because of the built in VMs and because it is Linux. Pay google for support and no updates unless there is something critical.
edit: Lots of Microsoft lovers here lol. And missing the point which is that using the most well known consumer OS for critical stuff like keeping flights going is begging for trouble.
The disaster likely happened because Crowdstrike didn’t do any phased rollouts or testing, which would have picked up a glitch like these before it could brick countless millions of systems. Blaming Microsoft for what is most likely gross negligence from a major cybersecurity firm is downright disingenuous.
Also, recommending an overglorified web browser baked into an OS which can only run web and Android applications to run critical infrastructure is downright laughable, ESPECIALLY when Google are known for their downright nonexistent customer support.
People use Windows because it’s the most well-known and used OS on the market, and because Microsoft is a multi-billion dollar tech giant with a dedicated customer support and tech team to fix issues posthaste.
blaming Microsoft
I’m not blaming Microsoft. I am blaming companies for using Microsoft for critical systems.
Also, recommending an overglorified web browser baked into an OS which can only run web and Android applications to run critical infrastructure is downright laughable,
You not understanding that ChromeOS is a highly secure Linux computer is that can run any Linux program is downright laughable ignorance.
ESPECIALLY when Google are known for their downright nonexistent customer support.
Their software is way too widely used to provide you with free customer support. Microsoft is no different.
Mainly people are down voting you because Linux had also been affected by Crowdstrike before. Only a few months ago at that. There aren’t any more defenses in Linux systems against this kind of problem than there are in Windows ones. This isn’t even strictly speaking a security issue either. It’s more like a bug in critical software that just happens to be security related. It’s a bit like when that Grub update broke some people’s arch setups.
It’s not that Linux can’t have security problems. I still remember the very first internet virus in 1987 that traveled thru Unix machines. But Windows is the worst OS for critical systems precisely because it is the most common OS. Anything is better than windows. Linux, MacOS, or even an old IBM mainframe OS and those awful tn3270 terminals. Also, Chrome OS in particular has VMs instead of other VMs. It really is designed to be much more secure than Windows.
It’s more like a bug in critical software that just happens to be security related.
And so the cure is the same as the disease. Or actually worse in this case. The very fact that systems were constantly updated was itself the problem rather than the solution to the problem. How did nobody realize this was going to happen sooner or later?
Linux had also been affected by Crowdstrike before.
I’m guessing Crowdstrike issues a lot more Windows updates than Linux updates?
I’m guessing Crowdstrike issues a lot more Windows updates than Linux updates?
Not really. Linux is used for critical servers everywhere. No reason to update it less often.
It’s not that Linux can’t have security problems. I still remember the very first internet virus in 1987 that traveled thru Unix machines. But Windows is the worst OS for critical systems precisely because it is the most common OS. Anything is better than windows. Linux, MacOS, or even an old IBM mainframe OS and those awful tn3270 terminals. Also, Chrome OS in particular has VMs instead of other VMs. It really is designed to be much more secure than Windows
This isn’t a hacking attempt. It’s not a security breach. None of the “Windows is more common” stuff is actually valid in this case. The fact it’s not actually true is even more funny. When it comes to servers and smartphones, and the total number of devices in general, Linux outnumbers Windows. Linux isn’t actually niche in the slightest, only purists running Arch or Ubuntu think that because they ignore any Linux they don’t like, like Android.
You also don’t understand anything about ChromeOS security either. They don’t use VMs for system security. Early Chromebooks actually had virtualization disabled! Sandboxing and virtualization aren’t the same thing. The reason it’s secure is largely because it can’t do anything, it uses an a/b root system, and it has secure boot by default. It’s not that fancy anymore.
Chrome the web browser also has sandboxing on Windows, and modern Windows uses secure boot. Edge and Chrome have the same foundation btw. What it’s missing is the immutable a/b root system, and the fact Windows allows running arbitrary executables when ChromeOS doesn’t. There are actually tools for making Windows immutable, and with group policy or things like S mode you can restrict who can run what executables. Meaning with the right settings it’s almost as secure as ChromeOS. Even more funny Windows actually does use virtualization based security. So you have that backwards too.
Stop talking about shit you don’t understand and learn about it instead.
This isn’t a hacking attempt.
No but it is the result of trying to stop hacking attempts.
They don’t use VMs for system security.
They do. A major reason they use them is to make ChromeOS way more secure than windows.
Linux isn’t actually niche in the slightest
It’s fragmented. There is no single version
Stop talking about shit you don’t understand and learn about it instead.
Stop being a jackass and learn to communicate in civilized fashion.
with group policy or things like S mode you can restrict who can run what executables.
Companies don’t run windows in S mode and every OS has group security.
None of the “Windows is more common” stuff is actually valid in this case.
When I learned that companies are actually letting Cloudstrike download the equivalent of KERNAL MODE code into their critical systems I was dumbfounded. Who could have possibly thought that was a good idea? This was absolutely a disaster that was just waiting to happen.
However, if it happened on Linux, it could have been immediately bypassed.
Automatically reverting the kernel wouldn’t do anything as the kernel nor the module Crowdstrike uses were updated. Rather the file the module reads was updated and replaced with a corrupted version that causes the module to crash when it tries to read it.
There is a great video explaining the basics of what happened here: https://youtu.be/wAzEJxOo1ts?si=_agkbdBHJnhQmbdP
Microsoft already have a mechanism to disable problematic modules on next boot. Problem being that Crowdstrike registers itself as an essential driver, as they don’t want the system to boot without it for security reasons.
You keep saying Chrome OS uses VMs for security. Unless something has seriously changed since I last read up on their security mechanisms they don’t. Maybe something has changed. Do you have any evidence? If not you’re just talking out of your arse.
Sure I’ve got lots of evidence.
https://www.security.org/antivirus/chromebooks/
[There’s no question that, when it comes to viruses and other forms of malware, Chromebooks are safe. How safe? Well, the website CVE Details1 lists just 55 vulnerabilities for Chrome OS. Compare that to 1,111 vulnerabilities for Windows 10, and a whopping 2,212 for Mac’s OS X; with five percent as many vulnerabilities as its closest competitor, it’s a pretty simple matter to declare Chromebook the safest option…there’s no question that Chromebooks are among the most secure computers you can buy]
55 vulnerabiilites for Chrome OS vs 1111 vulnerabilities for Windows. Huge difference.
Rather the file the module reads was updated and replaced with a corrupted version that causes the module to crash when it tries to read it.
Yes it was a ridiculous system to have kernel mode code on the filesystem. Even if a bad pointer didn’t crash the system a hacker could have put in their own code. And yes such a terrible security system would have affected Linux too. But with ChromeOS, the system is already secure. No need to use a terrible security system like Cloudstrike in the first place.
No you don’t have any evidence at all. You were specifically speaking about Chrome OS using VMs inside VMs. That article doesn’t mention VMs once.
I never once disputed that it was more secure than an average Windows installation, because frankly that’s obvious. What you don’t seem to understand is what can be done to lock down modern Windows and Linux systems.
Yes it was a ridiculous system to have kernel mode code on the filesystem. Even if a bad pointer didn’t crash the system a hacker could have put in their own code. And yes such a terrible security system would have affected Linux too. But with ChromeOS, the system is already secure. No need to use a terrible security system like Cloudstrike in the first place.
For one the same article you are referencing talks about using anti-malware on ChromeOS as Chrome OS isn’t malware proof. Though I don’t think it’s possible for Chrome OS to break so badly from one of these products.
ChromeOS though isn’t actually suitable for running servers like Windows and Linux are. It can’t do nearly the same number of things. It’s a bit like comparing a knife to a safety razor. One is safer for shaving sure, however the other one can be used for cooking, hunting, wood work, etc.
Second all kernel mode code lives on the filesystem. How did you think it worked? On Linux and Windows the kernel itself needs storing somewhere, as do the modules.
You keep showing me again and again that you don’t understand the world of computers and modern IT infrastructure. Do you even have any qualifications or work experience in IT?
Edit: I actually did some research myself. ChromeOS can use a Virtual Machine to run Linux software, but not in it’s default configuration. There is also none of this VMs inside VMs stuff you were talking about. If you want to see virtualization really put to work look at a modern server setup or something like Qubes OS.