+-----------------+
| . local server |
+-.---------------+
< . >
< . >
< . >
< . >
< . >
+-.-----------------------+
| . serveo/localhost.run |
+-.-----------------------+
< . >
< . > +----------------------+
< . > | . raw data |
< . > | < . > encrypted data |
< . > +----------------------+
+-.----------+
| . clients |
+------------+
hellow,
i wanna host things (nextcloud, bin, syncthing) myself but im under cg nat so i cant do it the regular way. i have to tunnel my way out. the only concern is that, the raw data is readable by the ssh server (ie. serveo/localhost.run), but i dont anyone elses eyes on my data
sorry for my broken english.
edit:
- syncthing (solved): https://docs.syncthing.net/users/untrusted.html
- bin (solved): https://github.com/HemmeligOrg/Hemmelig.app?tab=readme-ov-file#features
- nextcloud: ???
please clarify me.
if i setup a vpn which provides encryption on my local server, can i go like this
+------------------+
| . local server |
+-< . >------------+
<< . >>
<< . >>
<< . >>
<< . >>
<< . >>
+-< . >----------------------+
| < . > serveo/localhost.run |
+-< . >----------------------+
<< . >>
<< . >> +-------------------------------------+
<< . >> | . raw data |
<< . >> | < . > vpn encrypted data |
<< . >> | << . >> vpn encrypted data over tls |
<< . >> +-------------------------------------+
+-< . >-------+
| . clients |
+-------------+
sorry i dont know how to express this in words
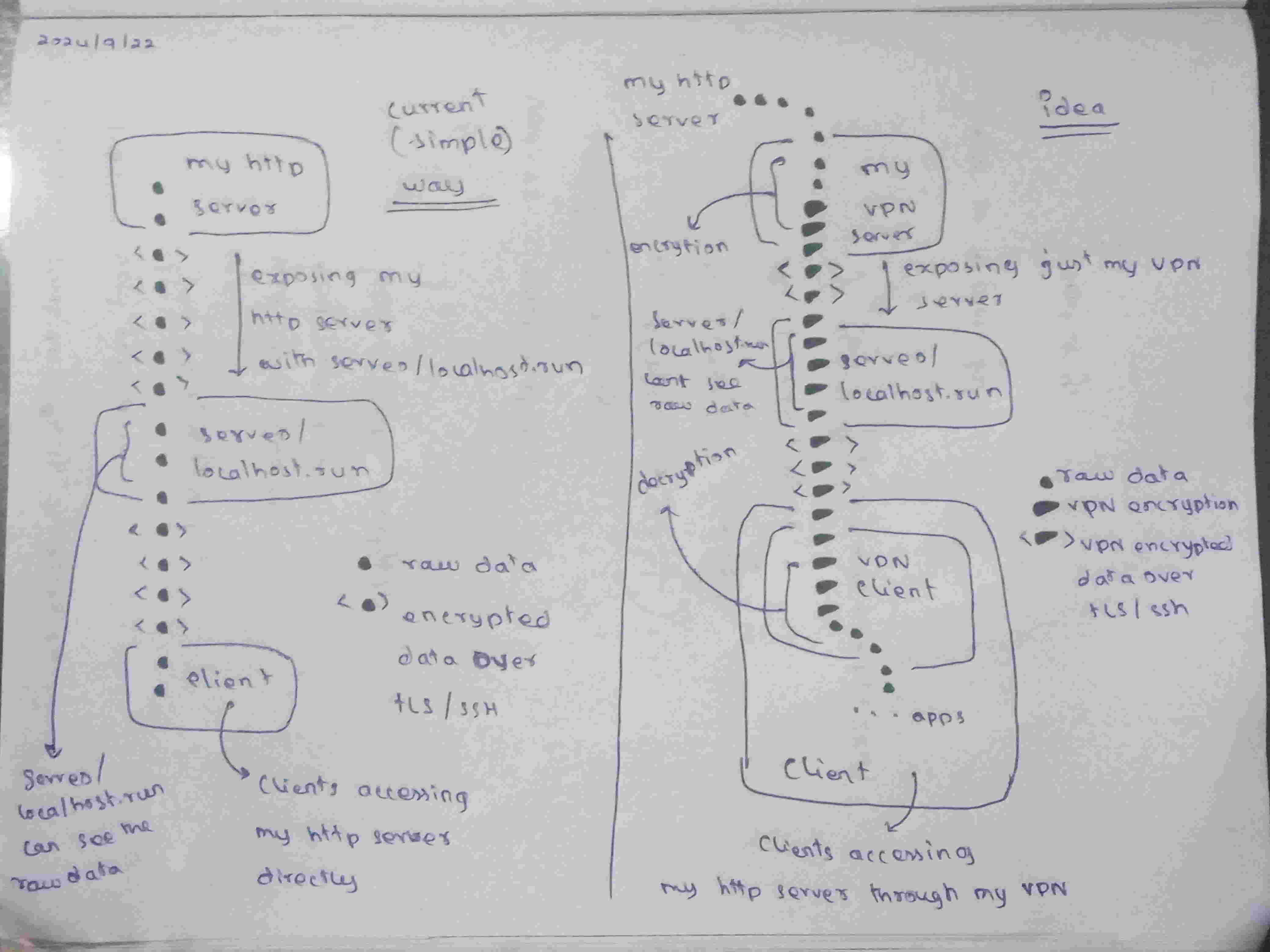
this is what i was trying to say. so the idea, is that okay?


I personally rent the cheapest VPS I could find and put Tailscale on it. My server at home then connects to that Tailscale network and the VPS runs nginx acting as a proxy forwarding everything to the server through Tailscale.
Besides having no annoying networking issues it also has the benefit that I can move houses without having to update A records to have the domain point to the new IP address because the VPS IP ofc remains the same.
Another (and to some degree more flexible AND simpler) solution is rathole: still requires you to host it somewhere, but it’s got a little more flexibility.
Edit: I’m not a fan of VPN tunnels in general, because for most people all you’ve done is made a remote server that, if it’s compromised, will have unfettered and complete access to your internal network via the VPN tunnel.
There are ways to mitigate that but, for what I suspect is the majority of people asking about how to do this, they’re outside of a reasonable technical ask.
(Rathole works similar to an argo tunnel, in that it initiates a connection to the VPS, and then passes traffic limited to a specific port or application back and forth, rather than being a nice open tunnel.
wait. please clarify me.
if i setup a vpn which provides encryption on my local server, can i go like this
sorry i dont know how to express this with words
Yes